My opinion: QNAP devices are insecure!
Inhaltsverzeichnis
- My opinion: QNAP devices are insecure!
- Too much network services running by default
- Firmware updates often unstable
- Error culture at QNAP missing? Workaround culture!
- Incomplete information about security issues
- Outdated software in use
- QNAP Apps running as privileged user
- Second factor authentication: a hoax?
- Conclusion: QNAP NAS TS-431+ can not be considered as secure
I own 2 QNAP devices, one TS-431+ and another TS-231P lent from QNAP itself. Furthermore I care about 2 additional devices. My experience with QNAP are now over 4 years. In this article I like to point out why QNAP is applying bad practices when it comes to security issues and why I would not recommend to use them in an insecure environment.
I am not a „security expert“, what I discovered are only the obvious problems.
Too much network services running by default
If you buy a QNAP NAS you will see a lot of services activated per default. This makes the NAS itself vulnerable for attacks and increases the attack surface. This is not only my opinion, even QNAP recommends to deactivate unused services.
We recommend that users disable services that they currently do not need to reduce the likelihood of being attacked.
QNAP security FAQ
The problem simply is that they are activated if you get a brand new NAS from QNAP and my guess is that most users are unaware of this risk and will leave them activated. Why not deactivate all the services and if a user will need one let him activate it manually?
-
14%
 QNAP NAS, no HDD/SSD, ARM processor, NPU | TS-233, 2-bay, 2GB RAM, 1GbE *209,00 € 180,78 €
QNAP NAS, no HDD/SSD, ARM processor, NPU | TS-233, 2-bay, 2GB RAM, 1GbE *209,00 € 180,78 € Stand von: 27. Juli 2024 12:44 *2
Stand von: 27. Juli 2024 12:44 *2 -
27%
 QNAP TS-264-8G NAS N5095 8 GB (TS-264-8G) *558,11 € 409,00 €
QNAP TS-264-8G NAS N5095 8 GB (TS-264-8G) *558,11 € 409,00 € Stand von: 27. Juli 2024 12:44 *2
Stand von: 27. Juli 2024 12:44 *2 -
23%
 QNAP Systems TS-453E-8G 4 Bay 8 GB DDR4 *819,91 € 632,45 €
QNAP Systems TS-453E-8G 4 Bay 8 GB DDR4 *819,91 € 632,45 € Stand von: 27. Juli 2024 12:44 *2
Stand von: 27. Juli 2024 12:44 *2 -
18%
 Qnap TS-433-4G NAS System 4-Bay *474,81 € 388,59 €
Qnap TS-433-4G NAS System 4-Bay *474,81 € 388,59 € Stand von: 27. Juli 2024 12:44 *2
Stand von: 27. Juli 2024 12:44 *2 -
 Qnap TS-464-8G | 4-Bay, PCIe Gen3, 2.5GbE Tower NAS *591,37 €
Qnap TS-464-8G | 4-Bay, PCIe Gen3, 2.5GbE Tower NAS *591,37 € Stand von: 27. Juli 2024 12:44 *2
Stand von: 27. Juli 2024 12:44 *2
Firmware updates often unstable
To mitigate most attacks your firmware should be kept up to date. The problem is that QNAP has serious problems with its firmware quality. In 2018 they revoked at least 7 firmwares. Reasons which prevent me to use the newest firmware are:
- they contain major flaws which make the system unstable
- there is no communication about revoked firmware
- no communication about the problem
- no communication about the removal of the firmware
I always wait at least one week before installing the new firmware to make sure that it will not harm my system.
Error culture at QNAP missing? Workaround culture!
It looks like that they are not able to deal with problems on their devices in a professional manner. This is the case when it comes to the revoked firmwares. But there are some other points which should be mentioned. The QNAP support prefers workarounds instead of fixing the root cause of a problem. Examples for that:
- Backup software may lead to corrupt versioning
- Antivirus fails to update
- No SSL / HTTPS for remote support
In all these examples no permanent solution is provided.
Incomplete information about security issues
Security holes are a constant threat in the IT industry and of course QNAP devices are also effected. It is important that a company can deal with them and gives clear instructions to its user base. Here a list with questions which should be answered by a security advisory:
- What is the attack vector / the security hole which allowed the attack?
- Which software is affected?
- Which software version is affected?
- How can I identify an attack on my device?
- What are the steps to circumvent the problem?
Nearly none of these questions are properly answered in QNAP security advisories.
Lets take the QSnatch malware. Here is the advisory by QNAP:
Security Advisory for Malware QSnatch
They only give general advises on how to keep your system safe like keep your software up to date:
Update QTS to the latest available version. Install and update Malware Remover to the latest version. Install and update Security Counselor to the latest version. Update your installed QTS applications to the latest versions if available in the App Center.
Security Advisory for Malware QSnatch
This is general good practice but its nothing related to QSnatch. Furthermore no attack vector is mentioned and the exact software versions which are vulnerable are also kept secret. They also mix up the steps which you should consider if you have been attacked and the steps which you should do to prevent an attack. They also miss to give you the instructions to detect an attack.
-
 Synology DiskStation DS224+ 2 Bay Dekstop NAS *338,00 €
Synology DiskStation DS224+ 2 Bay Dekstop NAS *338,00 € Stand von: 27. Juli 2024 12:44 *2
Stand von: 27. Juli 2024 12:44 *2 -
13%
 Synology DS223J 2 Bay Desktop NAS, weiß *219,99 € 192,00 €
Synology DS223J 2 Bay Desktop NAS, weiß *219,99 € 192,00 € Stand von: 27. Juli 2024 12:44 *2
Stand von: 27. Juli 2024 12:44 *2 -
 Synology DS923+ 4 Bay Desktop NAS Ryzen R1600 Dual-Core *588,54 €
Synology DS923+ 4 Bay Desktop NAS Ryzen R1600 Dual-Core *588,54 € Stand von: 27. Juli 2024 12:44 *2
Stand von: 27. Juli 2024 12:44 *2 -
15%
 Synology DiskStation DS723+ NAS/Storage Server Tower Ethernet LAN Black R1600 *549,99 € 469,95 €
Synology DiskStation DS723+ NAS/Storage Server Tower Ethernet LAN Black R1600 *549,99 € 469,95 € Stand von: 27. Juli 2024 12:44 *2
Stand von: 27. Juli 2024 12:44 *2 -
 Synology DS224+ 2-Bay Diskstation NAS (Intel Celeron J4125 4-Core 2.0 GHz 2GB DD... *599,90 €Stand von: 27. Juli 2024 12:44 *2
Synology DS224+ 2-Bay Diskstation NAS (Intel Celeron J4125 4-Core 2.0 GHz 2GB DD... *599,90 €Stand von: 27. Juli 2024 12:44 *2
Outdated software in use
Some examples here from my QNAP TS-431+ which is still in maintenance:
Linux kernel
Linux NAS12TB 4.2.8 #2 SMP Wed Jul 29 05:53:49 CST 2020 armv7l unknown
This kernel version dates back to 2015. I bought the NAS end of 2016. Now we have 2020.
My Raspberry Pi 4 outputs this version:
Linux raspberrypi 5.4.51-v7l+ #1327 SMP Thu Jul 23 11:04:39 BST 2020 armv7l GNU/Linux
QVPN (OpenVPN)
QVPN offers several protocol options. One of them is OpenVPN. In 2020 they use a three year old Version (august 2020):
Output from my NAS
OpenVPN 2.4.3 arm-unknown-linux-gnueabihf [SSL (OpenSSL)] [LZO] [LZ4] [EPOLL] [MH/PKTINFO] [AEAD] built on Nov 22 2019
2.4.3 has been released in 2017
The libraries used are also not up to date.
Output from my RPi 4
OpenVPN 2.4.7 arm-unknown-linux-gnueabihf [SSL (OpenSSL)] [LZO] [LZ4] [EPOLL] [PKCS11] [MH/PKTINFO] [AEAD] built on Feb 20 2019
2.4.7 has been released in 2019
AntiVirus (ClamAV)
WARNING: Your ClamAV installation is OUTDATED!
WARNING: Local version: 0.102.2 Recommended version: 0.102.4
QNAP Apps running as privileged user
QNAP does not offer a secure user concept. Nearly all processes are running as „admin“ user and all apps installed via the QNAP App store are running as „admin“ user.
The consequence is that if one service or process can be hijacked the attacker can gain full admin access on your device.
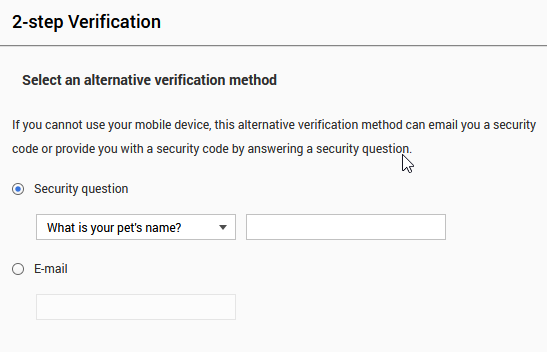
Second factor authentication: a hoax?
I tried to increase the security by enabling the 2FA on my NAS. But I discovered that you are forced to use an insecure fallback mechanism. You can either specify a mail address or a security question. In my opinion this weakens the security of the second factor.
Conclusion: QNAP NAS TS-431+ can not be considered as secure
Considering the mentioned critics I personally would not consider my QNAP NAS as secure at all. Nevertheless you can help yourself and configure your NAS as secure as possible by following this video:
Please accept YouTube cookies to play this video. By accepting you will be accessing content from YouTube, a service provided by an external third party.
If you accept this notice, your choice will be saved and the page will refresh.